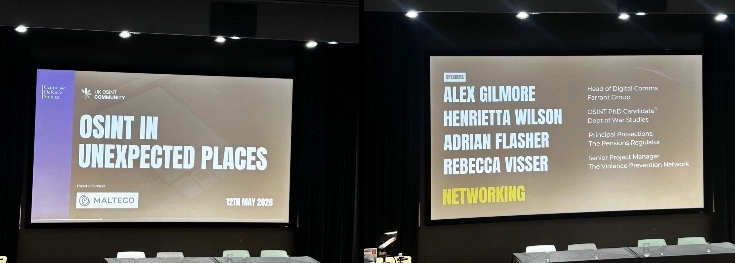
Last night’s UK OSINT Community event, “OSINT in Unexpected Places,” made a strong case that public research methods are no longer confined to state-led investigations or media monitoring. Across reputation management, arms control, academia, complex prosecutions, and violent extremism prevention, the speakers emphasised how OSINT sits at the centre of decision-making in areas where evidence is partial, narratives are contested, and the stakes are high.
A recurring theme was that OSINT is not just about collecting information, but about understanding the environments in which perception forms and spreads. That was especially clear in Alex Gilmore’s talk on OSINT in reputation management at Farrant Group. For governments, reputation shapes tourism, investment, diplomatic standing and soft power. For companies, it affects sales, customer loyalty, litigation risk and regulatory attention. For individuals, it can determine credibility, opportunity and influence. In all three cases, OSINT helps map the channels through which opinion moves and identifies where hostile narratives begin.
What made this particularly useful was the distinction between threat detection and response. OSINT-led work can identify the source of a hostile narrative, trace how it is being amplified, and assess the threat. Reputation management teams then decide how to respond. That might mean briefing legitimate journalists, attributing and taking down anonymous attack sites, or reporting impersonation campaigns to platforms for removal.
The next speaker was Henrietta Wilson, Lead Editor of “Digital Investigations in the Age of Google,” Freelance WMD expert and PhD candidate at Kings College London. She shifted the focus to transparency, accountability and the challenges of working in technical and opaque fields such as WMD, arms control and disarmament. Her argument was that OSINT can shed some light on one of the most politically important questions in these areas: who has what, and how do we know? Satellite imagery, for example, has been used to detect North Korea’s WMD activity by assessing environmental indicators such as snow melting at unusual times of year. These kinds of observations matter because they create forms of accountability where direct access is impossible.
At the same time, she highlighted a major challenge: 'OSINT' is often distrusted because the term is so broad. That makes methodological clarity essential. She further emphasised several core truths as correlates of this:
- If a report is to be useful to decision-makers, its sources and workflows need to be transparent enough that others can reproduce the work, understand its limits and see where gaps remain.
- Emphasise NEGINT, and acknowledge uncertainty rather than over-claiming
- Ethical guidance —such as the Berkeley Protocol or Bellingcat’s own standards— gives the field a framework to operate in
Adrian Flasher’s presentation on the prosecution of complex cases brought the conversation into the legal arena. He drew a useful line between cyber-dependent crime, which exists only because of ICT systems, and cyber-enabled crime, where traditional offending is amplified through technology. The threat landscape includes lone actors, organised criminal groups, and state-linked actors, with the rise in ransomware and other forms of cybercrime continuing to blur those categories. He shared an interesting case study on a fifteen year old, who sold his DDOS-for-hire service to bad actors across the globe; not for money, but for the love of the game.
Flasher also touched on the idea that OSINT often serves as a way to mirror evidence that cannot be shared directly in court, while still building a persuasive case around it.
That led to one of the most memorable observations of the evening: technical brilliance is not enough to secure a conviction. Prosecutors also need a story that is understandable, coherent and convincing. In that sense, OSINT is not merely forensic, it is narrative infrastructure. It turns dispersed traces into a case that a non-technical judge or jury can follow. The mention of crypto was equally practical. The notion that cryptocurrency offers anonymity remains overblown; in reality, agencies such as the NCA and other authorities have substantial tools to identify the person behind an account. The myth of invisibility is often stronger than the reality.
Rebecca Visser’s talk on violent extremism prevention broadened the discussion again, showing how OSINT can support primary, secondary and tertiary prevention. Primary prevention is upstream work, including education and training designed to reduce the risk of radicalisation before it takes root. Secondary prevention focuses on identifying vulnerability among those exposed to extremist content, assessing propensity to action, and understanding how online interaction may lead to offline risk. Tertiary prevention comes after an incident, when the objective is to disengage individuals from violent communities and support reintegration into society.
Her case studies illustrated how OSINT can help disrupt plots, by mapping networks, actors and patterns of behaviour. Projects such as Stop Hate Brazil show how monitoring can reveal networks long before they become operational threats. Her discussion of Shia-aligned Iranian groups also underscored the importance of reading organisational structure from digital traces, including misspellings and decentralised language that can indicate loose command structures.
Taken together, the event showed OSINT as a disciplined way of turning public information into actionable insight across distinct domains. The common thread was clear. Whether the problem is hostile disinformation, weapons monitoring, courtroom evidence or extremist mobilisation, OSINT is central to understanding how power operates in the public shadow and how institutions can respond before potential harm becomes irreversible fact.